Highlights:
- Advertised as legitimate tools, Remcos and GuLoader are malware in disguise, heavily utilized in cyberattacks
- Check Point Research (CPR) has uncovered evidence that the distributor is deeply entwined within the cybercrime scene, leveraging their platform to facilitate cybercrime, while making a profit
- CPR has identified “EMINэM” as one of the cyberciminals behind the distribution Remcos and GuLoader
- CPR has disclosed its findings to the relevant law enforcement entity
“Legit” software becomes cybercrminals’ preferred choice
In an alarming trend highlighted in Check Point’s 2023 Mid-Year Security Report, seemingly legitimate software has become the preferred choice of cybercriminals. Notable examples are the Remcos Remote Access Trojan (RAT) and GuLoader, both advertised as legitimate tools but heavily utilized in cyberattacks, consistently ranking among the most prevalent malware. Although their sellers claim lawful usage, CPR found a strong connection between these tools and cybercrime.
While Remcos struggles to evade antivirus detection, GuLoader acts as its ally, helping it bypass protection measures. CPR discovered that GuLoader is rebranded and sold as a crypter, ensuring Remcos’ payload remains fully undetectable by antiviruses. Strikingly, the same administrator manages the platform, selling both tools while operating the official website and Telegram channels for Remcos. CPR found compelling evidence that this individual not only employs malware like Amadey and Formbook, but also uses GuLoader to shield against antivirus detection. Domain names and IP addresses associated with the Remcos and GuLoader seller appear in malware analyst reports.
Guloader and Remcos are among the leaders of the (infamous) pack
In July’s Most Wanted malware report, CPR reported that RAT Remcos rose four places due to trojanized installers. Remcos now sits at third place after threat actors created fake websites last month to spread malicious downloaders carrying the RAT.
First detected in 2016, Remcos is a RAT that is regularly distributed through seemingly authentic Microsoft documents or downloaders that are actually malicious. It has been most recently observed in a campaign involving the Fruity malware downloader. The objective was to lure victims to download the Fruity downloader, which installed different RATs such as Remcos (known for its ability to gain remote access to the victim system) to steal sensitive information and credentials and conduct malicious activity on the user’s computer.
GuLoader and Remcos in 2023 – Finance and Education sectors key targets
According to intelligence from Check Point ThreatCloud AI
- GuLoader: In the Finance/Banking sector, an average of 2.4% of organizations globally were affected monthly (equivalent to 1 out of 41 organizations)
- GuLoader: most substantial impact in the EMEA region, with a monthly average impact of 4.7% (equivalent to 1 out of 21 organizations)
- Remcos: In the Education/Research sector, an average of 2.8% of organizations globally were affected monthly (equivalent to 1 out of 35 organizations)
- Remcos: greatest impact in the APAC region, with a monthly average of 2% (1 out of 50 organizations)
Deceitful Distributor is actually part of the illegal operation
CPR’s investigation leads to a clear conclusion: the seller/s of Remcos and GuLoader are well aware of their software being embraced by cybercriminals, despite their disingenuous claims. CPR aims to expose the criminal responsible for selling these tools, revealing their social networks and uncovering the significant illicit income generated through these activities. This study underscores the serious threat posed by dual-use software and highlights the need for heightened vigilance against such deceptive practices in the cybersecurity landscape.
In 2020, CPR exposed an Italian company that was selling the CloudEyE product through the website securitycode.eu and revealed its direct affiliation with GuLoader. Our findings forced the creators of CloudEyE to temporarily suspend their operations. On their website, they posted a message saying that their service is designed to protect intellectual property, not to spread malware.
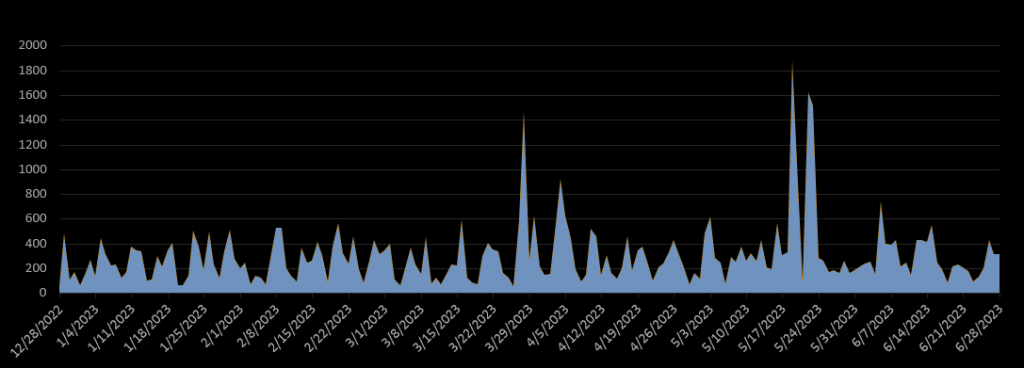
After a few months, their website resumed the sale of CloudEyE. Soon afterwards, CPR observed an increase in the number of new GuLoader attacks in our telemetry, as well as the appearance of new versions. Currently, we monitor dozens of new GuLoader samples on a daily basis.
In our previous article about the latest versions of GuLoader, we purposefully omitted any connection between CloudEyE and the new version of GuLoader because we observed the distribution of GuLoader under an alternative name “The Protector” on the website named “VgoStore.” VgoStore, as it turns out, is closely related to Remcos.
Remcos is a well-known remote surveillance tool, marketed for legitimate tracking and monitoring purposes. Since its appearance in 2016, we have been monitoring Remcos in many phishing campaigns. In addition to its typical remote administration tool features, Remcos includes uncommon functionalities such as man-in-the-middle (MITM) capabilities, password stealing, tracking browser history, stealing cookies, keylogging, and webcam control. These features go beyond the typical scope of a RAT and suggest a more intrusive and malicious intent.
Investigative Outcomes
CPR’s investigation uncovered a clear connection between an individual known as EMINэM and two websites, BreakingSecurity and VgoStore. These websites openly sell Remcos and GuLoader, rebranded as TheProtect. Additionally, we have gathered evidence of EMINэM’s involvement in distributing harmful malware, including FormBook info stealer and Amadey Loader. Moreover, EMINэM exploits TheProtect to evade antivirus detection for his own malicious activities.
The apparent legitimacy of BreakingSecurity, VgoStore, and their products is merely a façade. EMINэM and those behind these platforms are deeply entrenched in the cybercriminal community, using their websites to facilitate illegal actions and profit from selling malicious tools.
This discovery emphasizes the ongoing need for constant vigilance and cooperation in the fight against cybercrime. Law enforcement agencies, cybersecurity professionals, and the wider community must collaborate to expose and neutralize such threats. By shedding light on individuals like EMINэM and their associated platforms, we strive to create a safer digital environment that better safeguards individuals, organizations, and the overall digital ecosystem.
CPR has disclosed its findings to the relevant law enforcement bureau for further investigation
Check Point Threat Emulation customers are protected against attacks from Guloader & Remcos. Threat Emulation provides comprehensive coverage of attack tactics, file-types, and operating systems. It protects against the type of attacks and threats described in this report.
Read the full research on https://research.checkpoint.com



21 comments
buy atorvastatin 40mg sale order atorvastatin 20mg online atorvastatin 80mg pills
ivermectina 6mg – how to get co-amoxiclav without a prescription sumycin 250mg without prescription
lasix 40mg cheap – candesartan 16mg drug buy captopril pill
order zidovudine – glycomet 1000mg cheap buy zyloprim 100mg pills
clozaril uk – purchase frumil online pepcid brand
buy quetiapine medication – buy generic bupropion over the counter buy eskalith sale
anafranil 50mg without prescription – pill imipramine 25mg order sinequan
order hydroxyzine 10mg online cheap – order atarax 10mg online endep 10mg generic
where to buy amoxicillin without a prescription – buy erythromycin generic order generic cipro 500mg
cleocin online order – terramycin 250 mg capsules buy cheap generic chloramphenicol
albuterol inhaler – brand fexofenadine theo-24 Cr for sale online
desloratadine 5mg oral – flixotide for sale online buy albuterol generic
order glyburide generic – where can i buy actos dapagliflozin 10mg usa
metformin 500mg uk – order metformin generic precose 50mg over the counter
rybelsus pills – desmopressin DDAVP
nizoral over the counter – buy sporanox 100mg online itraconazole online buy
purchase digoxin without prescription – buy furosemide paypal order lasix 100mg for sale
metoprolol generic – order metoprolol 50mg without prescription adalat for sale
buy hydrochlorothiazide online – norvasc 10mg brand buy bisoprolol cheap
order nitroglycerin pills – purchase lozol sale valsartan 160mg over the counter
crestor pills lighter – pravachol today caduet buy when